Off-Topic
Neues Büro - neues Netzwerk!
04. Juli 2019
Da wir ja vor kurzem in das coolste Büro in ganz Graz umgezogen sind, hatten wir die angenehme Nebenaufgabe unser Netzwerk neu zu planen. Was dabei herausgekommen ist, und warum wir nicht aufhören können uns jeden Tag darüber zu freuen steht in den folgenden Zeilen.
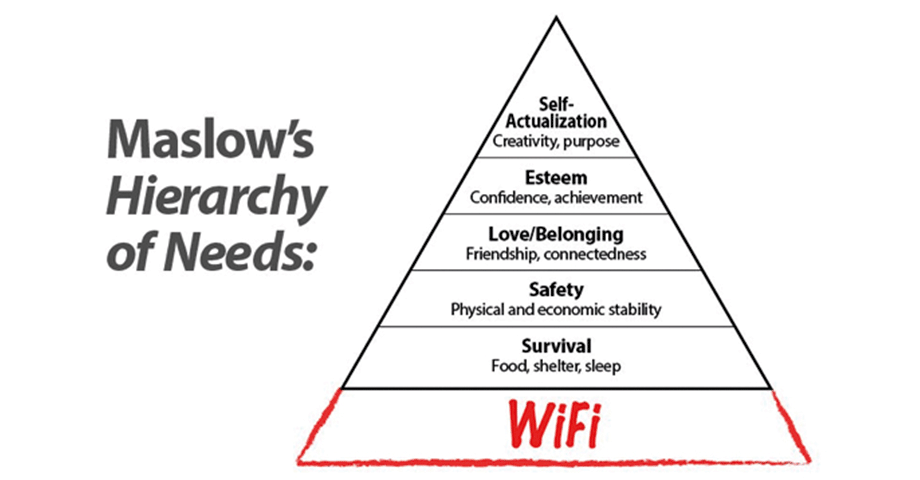
Hätte Abraham Maslow seiner Zeit schon gewusst, wie essentiell stabile und performante Netzwerk Verbindungen in unserem Alltag einmal werden, hätte er seine Bedürfnishierarchie wohl schon damals entsprechend anders gestaltet. Was im persönlichen Umfeld als lästiges Ärgernis auftreten kann, wenn sich das Handy ständig mit dem WLAN neu verbindet oder der Netflix Stream wieder nur bitweise hereintröpfelt. Kann in einem Unternehmen schnell bedeuten, dass im schlimmsten Fall der gesamte Betrieb stillsteht.
Und alle in die erzwungene Kaffeepause gehen müssen. Weil wir solche Horrorszenarien (zumindest aus Sicht der Netzwerk Admins, die in solchen Fällen auch gerne Pause machen würden) nicht heraufbeschwören wollen, haben wir uns im Vorfeld `ein paar´ Gedanken gemacht, wie wir unser Netzwerk für möglichst viele Herausforderungen wappnen können. Zusätzlich sollte das Ganze performant genug für die nächsten Jahre sein, dazu auch einfach erweiterbar und somit vor allem zukunftssicher, weiters alle möglichen coolen Features, die es derzeit gibt, unterstützen und gleichzeitig aber das Unternehmen nicht in die Insolvenz schicken.
Dankeschön
Ein riesengroßer Dank geht an dieser Stelle an unseren altehrwürdigen Netzwerk Großmeister, Bezwinger der VLANs und Experte für eh fast alles; Stefan B., für das gemeinsame Durchdenken und Abschätzen des gesamten Unterfangens, Setup und Betrieb sowie die wiederkehrende Begeisterung wenn wir neues `Spielzeug´ im Rack anschließen können. Er war es auch, der im alten Büro das Wunderwerk aus einem LTE Router und zwei ADSL Leitungen zu einer brauchbaren WAN Verbindung verheiratet hat, die bis zu unserem Auszug fleißig gewerkelt haben.
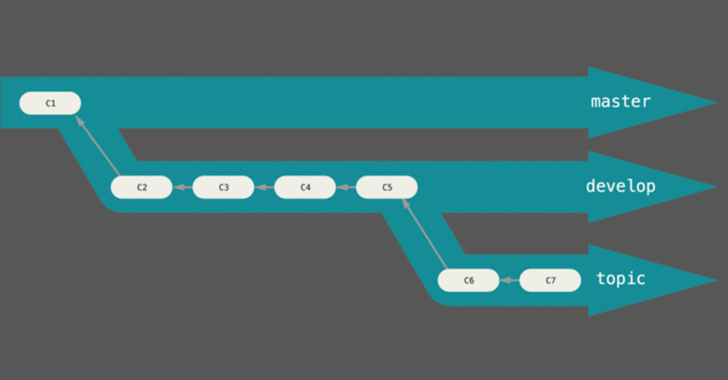
Auf dem Hauptrouter lief auch ein VPN Server, dessen Konfiguration schon in einem älteren Post beschrieben wurde, dahinter hing ein 24 Port Gigabit Switch und einige weitere `kleinere´ Switches, die das Netzwerk bis in den letzten Winkel und zum hintersten aller Arbeitsplätze des ehemaligen Büros kaskadierten. Ginge es gerade um Graphentheorie, so würde ich glatt den Vergleich mit einem Baum wagen – einem, nun ja, `besonderen´, keineswegs balancierten und für meinen Geschmack viel zu hohen Baum.
Aus alt mach neu, aus Baum mach Stern
Und so machten wir uns ans Werk, als wir voller Motivation begannen, die Netzwerk Dosen am Grundrissplan des neuen Büros einzuzeichnen. Die folgenden Punkte lagen für uns dabei alle irgendwo zwischen `must-have´ und `nice-to-have´:
-
WAN per Lichtwellenleiter & Router der mit den entsprechenden Geschwindigkeiten mit Leichtigkeit klarkommt
-
Pro Arbeitsplatz mindestens ein Gigabit Anschluss, direkt zum Rack
-
Managed Switches und VLANs für unterschiedliche Segmente
-
Access Points (APs) die per Power over Ethernet (PoE) versorgt werden
Bei einer Anzahl von rund 25 Arbeitsplätzen verteilt auf vier Räume, einem Showroom, einem Besprechungsraum und drei bis vier APs hatten wir ursprünglich das Gefühl, wir würden mit einem 48 Port managed Switch schon großzügig ansetzen. Das änderte sich schnell. Nachdem wir in unserer Blauäugigkeit plötzlich über 80 Anschlüsse auf dem Plan vor uns sahen. Man plant ja schließlich zukunftssicher. Und wer weiß, vielleicht werden die Tische ja mal umgestellt, dann braucht man an den Stellen, an denen derzeit noch niemand sitzt auch Netzwerkanschlüsse und kein Kabel quer durch den ganzen Raum – nicht wenn es sich `so einfach´ vermeiden lässt, wie im Plan einfach mehr Anschlüsse einzuzeichnen. Und so waren es plötzlich zwei 48 Port Switches. Aus dem Baum wurde ein Stern, der seine Mitte halbwegs im Zentrum des Büros hat – der Platz für unser Rack und zugleich mein neuer Lieblingsort.
Auch das Bündeln mehrerer langsamer Leitungen bzw. einer LTE Verbindung mit vergleichsweise hoher Latenz wollten wir diesmal sein lassen und haben uns daher informiert, welche Optionen in der Welt des erleuchteten Glases auf uns warten. Nachdem wir von einem namhaften ISP hörten, dass die Versorgung mit Lichtwellenleiter an unserem Standort schlichtweg “nicht möglich” sei, teilte uns ein anderer beim Anruf der Business Hotline mit, dass es “[…] sehr wohl ginge, man aber die ganze Straße aufgraben müsse […]”, was, ”[…] je nach Distanz, mit Kosten von 10000 bis 20000 Euro verbunden […]” wäre. Ich denke, ich muss nicht erwähnen, dass diese beiden Anbieter somit für uns aus dem Rennen waren.
Citycom Graz
Wir haben es danach bei der Citycom Graz versucht (was wir gleich von Anfang hätten tun sollen) – und siehe da; einige Zeit später standen deren Techniker schon am Rack und spleißten freudig vor sich hin. Einer der beiden meinte, auf meine Frage `was denn da so an Speed möglich wäre´ nur, dass “[…] jede der einzelnen Fasern Gigabit” schaffe und sie “[…] im Bedarfsfall die übrigen 20 der 24 Fasern auch noch verbinden […]” könnten. Wir verwenden wohlgemerkt nur eine der vier installierten und selbst diese mit einem asymmetrischen Tarif mit 300Mbit Down- und 50Mbit Upload.
Future-proofing at its finest, quasi ?
Hardware
Fragen über Fragen: Welcher Router? Welche Switches? Welche Access Points? Welcher Hersteller? CLI oder GUI – why not both?
In Zeiten solch wichtiger Fragen fanden wir zum Glück Antwort bei unserem Orakel, das einem bei Suche nach unseren Kriterien für die Switches (manageable, 48 Port Gigabit, mindestens einmal 10Gbit) fast 200 relevante Produkte ausgespuckt hat. Zum Erscheinungszeitpunkt dieses Blogposts und davor, bei unseren `hochwissenschaftlichen´ Nachforschungen, führten diese Liste zwei Geräte von Ubiquiti Networks an. Zusätzlich geisterte mir noch immer ein Artikel eines ehemaligen Sysadmins, der sich zuhause sein (und definitiv auch mein) Traum-Setup aus Ubiquiti Geräten aufgebaut hatte, im Kopf herum.
Switches
Da wir bisher gute Erfahrungen mit Access Points und Router derselben Marke gemacht hatten, freuten wir uns über die beiden Ergebnisse. Jetzt nur mehr entscheiden:
Die Suche nach den Switches war der Anfang unserer Reise in die Tiefen des Kaninchenbaus aus EdgeMax und UniFi Produkten. Man könnte meinen, ich werde von Ubiquiti Networks bezahlt. Hier so über ihre Produkte abzuraven oder bekomme sie gratis zugeschickt. Aber das ist (leider noch) nicht der Fall. Könnte ja noch was werden, richtig? *looking at you, Ubiquiti* Die Komponenten sollten jedenfalls gut harmonieren. Was einer der Gründe war bei derselben Marke zu bleiben.
Weiters sollten sie feingranular konfigurierbar sein, andererseits aber nicht zu kompliziert. Die UniFi Reihe benötigt zur Konfiguration der Geräte immer eine Controller Software. Diese die verschiedenen Komponenten erst so richtig zum Leben erweckt, dafür aber auch schöne Graphen und detaillierte Einblicke in das Netzwerk erlaubt. Weitere Unterschiede gibt es beim Command Line Interface (CLI). Das bei EdgeMax Geräten viel umfangreicher und vor allem so wirkt, als sei es dafür vorgesehen, auch tatsächlich verwendet zu werden. Wir haben uns daher bei den Switches und unserem Router, für die EdgeMax Reihe entschieden. Da diese immer mit einem Webinterface kommen, über das die Konfiguration von statten geht.
Auch ohne einen Controller
Ergänzend bietet Ubiquiti auch Software an, über die EdgeMax Geräte verwaltet und überwacht werden können: UNMS – aber dazu später noch mehr. Somit hatten wir zwei Fliegen mit einer Klappe geschlagen, und preislich bestand kein signifikanter Unterschied zwischen den beiden Geräten. EdgeSwitch Lite 48 – wilkommen in unserem Netzwerk.
Ach ja, und weil die beiden Switches jeweils zwei SFP+ Ports besitzen, fanden wir, es wäre eine Schande, sie nicht zu verwenden und haben sie kurzerhand mit zwei Direct-attach-copper Kabeln, die zu einer link aggregation group (LAG) zusammengefügt wurden, verbunden. Könnte ja sein, dass zufällig 20 unterschiedliche Clients auf dem einen Switch mit 20 unterschiedlichen Ports auf dem anderen kommunizieren möchten. Zeitgleich. Mit voller Gigabit Geschwindigkeit. Jetzt könnten sie das jedenfalls.
Router
Beim Router wünschten wir uns, dass er im Rack montiert werden kann, wenn auch über einen Adapter, wie wir ihn aktuell verwenden, und dass die Leistung für einige Jahre in der Zukunft ausreichen würde. Ein SFP Port wäre nett, ebenso PoE Support – man weiß ja nie – andererseits wäre ein Nichtvorhandensein aber kein Ausschlusskriterium gewesen. Zwischen den ganzen Kandidaten unter den EdgeMax Geräten konnten wir allerdings die größeren der EdgeRouter ausschließen, da acht und mehr Anschlüsse, geschweige denn Modelle mit ausschließlich SFP(+) Ports wie der ER-8-XG, für unseren Anwendungsfall viel zu überdimensioniert wären.
In die engere Auswahl schafften es dadurch der ER-4 und ER-6P, die beide einen 1GHz schnellen QuadCore Prozessor und 1GB RAM besitzen, aber nicht übertrieben viele Ports für unsere Verhältnisse. Laut dem Buyers Guide fallen auch beide in die Kategorie `maximize performance´ und schlussendlich setzte sich der ER-6P durch, da er zusätzlich noch PoE unterstützt.
Access Points
Auch hier wurden wir bei Ubiquiti Networks fündig, diesmal aber bei Produkten in der UniFi Reihe. Die angebotene Flut an Access Points konnten wir auch wieder relativ einfach grob einschränken. Da die größeren Modelle wie der UAP-HD oder UAP-SHD für jeweils 1000 und mehr Clients pro AP ausgelegt sind. Das für unsere Bedürfnisse wiederum viel zu viel ist. Allerdings fiel uns der (damals) relativ neue UAP-nanoHD auf, der, im Gegensatz zu der etwas günstigeren AC Pro Serie, 4×4 MU-MIMO unterstützt und außerdem wegen seiner kleineren Bauweise leichter untergebracht werden kann, ohne wiederum den preislichen Rahmen zu sprengen. Ach ja, es wurden vier Stück davon.
Software
Die beiden folgenden Absätze zeigen jeweils die Controller Software zur Verwaltung von UniFi bzw. EdgeMax Geräten. Wir hoffen, dass es in Zukunft eine Möglichkeit geben wird, die beiden Systeme zumindest zur Auswertung von statistischen Daten und Ähnlichem miteinander verbinden zu können. Derzeit gibt es das aber leider noch nicht. *still looking at you, Ubiquiti*
UniFi
Wie weiter oben schon erwähnt, brauchen diese UniFi Geräte einen Controller über den ihre Konfiguration eingestellt und verteilt wird. Wir verwenden dafür einen Docker Container, der lokal auf einem Server läuft und nebenbei ein detailliertes Webinterface zur Auswertung von Statistiken bereitstellt. Zum Beispiel für die Anzahl von verbundenen Clients und deren übertragenen Datenmengen, aktuelle Verbindungsgeschwindigkeiten und eine errechnete Qualitätszahl. Basierend auf der Aufteilung an Clients pro Channel und diversen anderen Metriken. Zusätzlich werden darüber auch Firmware Updates an die Access Points ausgerollt, sowie die SSIDs der Drahtlosnetzwerke definiert.
Der Controller kümmert sich dann automatisch darum, dass die freien Channels gleichmäßig über die APs aufgeteilt werden. Sich somit gegenseitig möglichst wenig stören. Zusätzlich empfiehlt es sich, diese Verwaltung auf einem eigenen VLAN durchzuführen. Welches ebenfalls im Webinterface der Controller Software angelegt und für jeden AP eingestellt werden kann. Auf unserem Router läuft dann für das gewählte VLAN auch ein eigener DHCP Server. Dieser IP Adressen nur für das Management Netzwerk verteilt und in diesem Fall auch für die APs.
In den beiden Screenshots sieht man einen kleinen Teil der Übersicht und mögliche Einstellungen. Wir haben uns weiters auch dazu entschlossen das Gäste WLAN ebenfalls in einem eigenen VLAN einzuzäunen. Den Zugriff zu unserem internen Netzwerk mit allen Rechnern der Mitarbeiter zu unterbinden und nur Verbindungen zum Internet zu erlauben. Darum kümmert sich ebenfalls der Router.
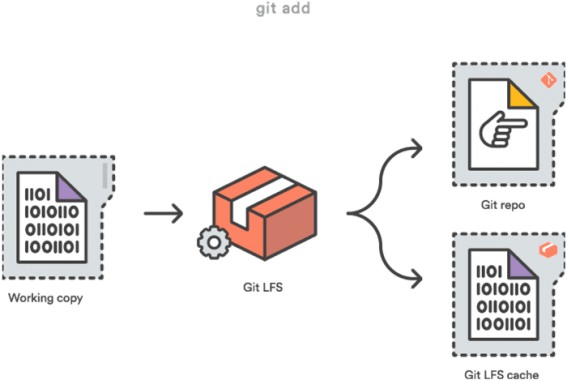
UNMS
Wie zuvor schon erwähnt, gibt es einen weiteren Software-Teil in unserem Setup. Der im Gegensatz zum UniFi Controller rein zur Visualisierung und Überwachung von EdgeMax Geräten dient. Wir verwenden hierbei Teile des Installationsskripts für UNMS von Ubiquiti, das auf github.com zu finden ist, wobei wir die Ports der Standard Installation angepasst haben.
Analog zum UniFi Controller kümmert sich auch UNMS darum. Wie neue Firmware Upgrades vorzuschlagen, per Klick auszurollen und auf den gewünschten Geräten zu installieren.
UNMS und der UniFi Controller erstellen außerdem jeweils automatisch Backups. Mit allen aktuellen Konfigurationen und erneuern diese, sobald Änderungen an den Einstellungen vorgenommen werden. Diese Einstellungen werden für den eingestellten Zeitraum aufbewahrt. Man kann diese auch manuell herunterladen und daher ohne großen Aufwand zu jeder vorherigen Konfiguration zurückkehren.
War’s das jetzt endlich?
Nicht ganz, ich habe ja noch gar nicht wirklich über unseren Router berichtet und der schuftet doch so fleißig. Also nochmal kurz hinsetzten und weiterlesen.
Wie oben kurz angeschnitten, haben wir versucht, die einzelnen Netzwerksegmente voneinander durch VLANs zu trennen. Was grundsätzlich schon mal eine gute Idee ist. Die Switches können portweise mit den unterschiedlichen VLANS tagged, excluded oder untagged werden. Das geht alles wunderbar über das Webinterface der Switches und des Routers (und sicher auch über das CLI). Dazu gibt es Unmengen an Tutorials und Erklärungen im Internet. Man kann die spannendsten Dinge damit fabrizieren, oder sich selbst schnell aussperren. Aber auch das reicht dann doch noch nicht ganz aus.
Zusätzlich sollten gewisse Verbindungen unter gewissen Voraussetzungen von einem zu einem anderen Netzwerkteil durchgelassen werden. Gut, dass jemand Stateful und Zonen-basierte Firewalls sowie die dazugehörigen zone-policies erfunden hat. Damit können Bereiche (zones) erstellt werden, die sich über mehrere reale aber auch virtuelle Interfaces erstrecken können. Um Verbindungen zwischen diesen verschiedenen Zonen zu erlauben oder zu verbieten gibt es die erwähnten Policies. Diese es beispielsweise ermöglichen, aus der Zone CF-LAN (unser genereller Bereich für alle Workstations) in die Zone WAN neue Verbindungen ins Internet aufzubauen (Aktion accept).
In die andere Richtung sind neue Verbindungsanfragen jedoch blockiert
Außer die eintreffenden Pakete gehören zu einer bereits aktiven Verbindung (Status established). Oder wurden als Antwort auf einen Request einer bereits bestehenden Verbindung empfangen (Status related). Verbindungen mit allen anderen Status (new oder invalid) werden hingegen sofort verworfen (Aktion drop). Einen super Artikel zum Einstieg in dieses Thema, in dem genauestens und mit Beispielen erklärt wird, wie eine solche Zonen-basiert Firewall aufgebaut sein kann, liefert Ubiquiti gleich selbst.